VACS
Visual Exploration of Threat Landscapes
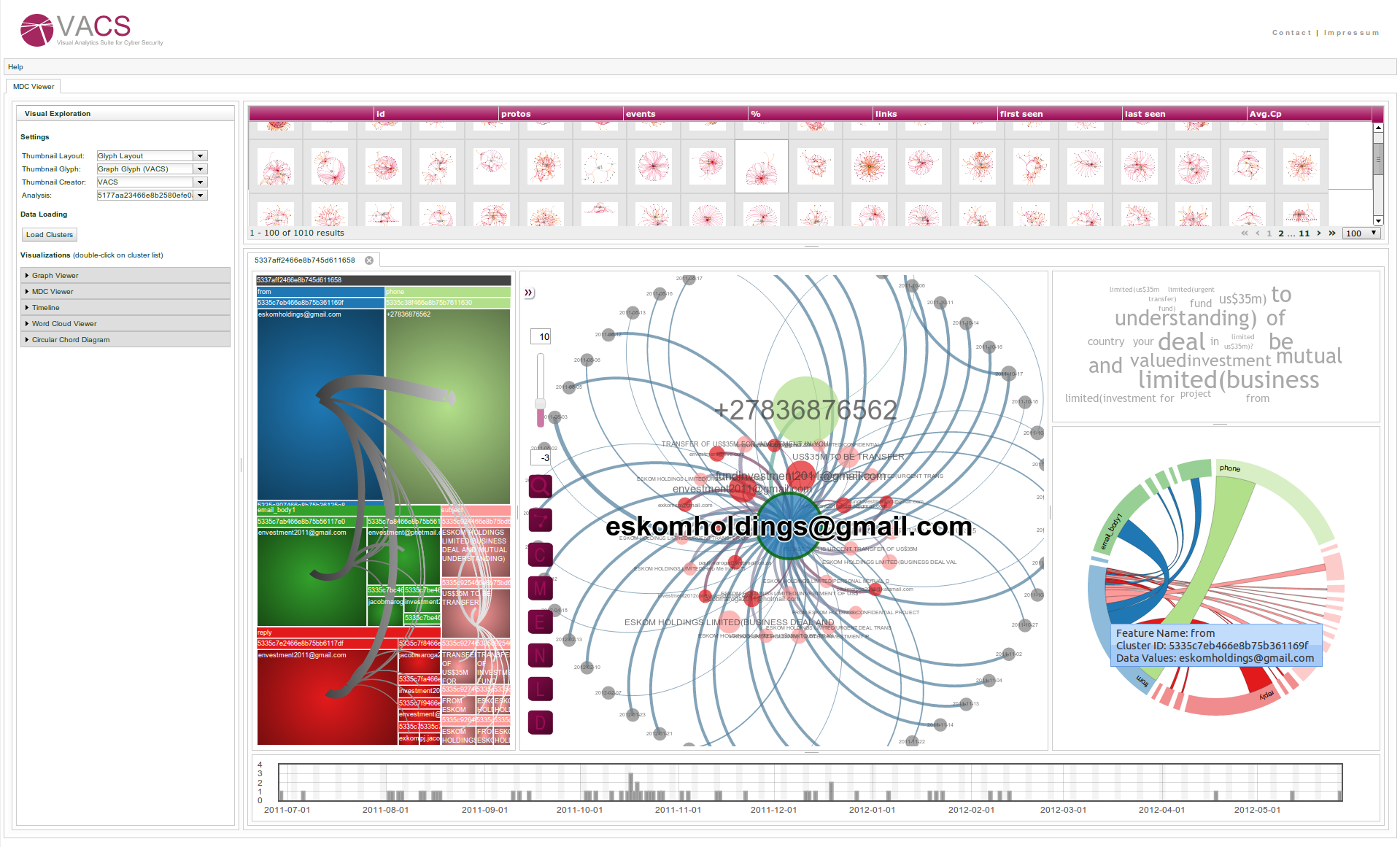
The analysis and exploration of emerging threats in the Internet is important to better understand the behaviour of attackers and develop new methods to enhance cyber security. Fully automated algorithms alone are often not capable of providing actionable insights about the threat landscape. We therefore combine a multi-criteria clustering algorithm, tailor-made for the identification of such attack campaigns with three interactive visualizations, namely treemap representations, interactive node-link diagrams, and chord diagrams, to allow the analysts to visually explore and make sense of the resulting multi-dimensional clusters. To demonstrate the potential of the system, we share our lessons learned in conducting a field experiment with experts in a security response team and show how it helped them to gain new insights into various threat landscapes.
Video: Using VACS for Visual Exploration of Multi-Dimensional TRIAGE Clusters
Video: Using VACS for Visual Exploration of VAST Challenge 2013
Visual exploration of cyber security datasets is an important and highly relevant field of research. To address the cyber security challenge of the VAST Challenge 2013, we utilized our novel Visual Analytics Suite for Cyber Security (VACS) to visually explore the given datasets using a combination of different visual representations. VACS primarily provides a dashboard view, host-based thumbnail overview and a querying interface to retrieve and drill down to investigate suspicious hosts.
Related Publications
- F. Fischer, J. Davey, J. Fuchs, O. Thonnard, J. Kohlhammer and D. A. Keim.
A Visual Analytics Field Experiment to Evaluate Alternative Visualizations for Cyber Security Applications. Proc. EuroVA International Workshop on Visual Analytics, 2014. (DOI, Paper) - F. Fischer and D. A. Keim. VACS: Visual Analytics Suite for Cyber Security – Visual Exploration of Cyber Security Datasets. VAST Challenge 2013 – Honorable Mention, 2013. (BibTeX, Paper, Slides)